
6connect uses port 22 to communicate with Secure64 infrastructure - please ensure that this is addressed in any ACLs/firewalls |
The initial setup of the Secure64 Authoritive server is as follows:
Make sure to add the line include: 6connect_nsd.conf to the nsd.conf file |
[authdnsadmin@Secure64DNS]# cat nsd.conf server: ip-address: 50.198.192.141 axfr-logfile: /axfr_log/axfr.log axfr-logfile-flush-count: 1 axfr-logfile-max-size: 100000 axfr-logfile-max-size: 10 request-logfile: /request_log/request.log request-logfile-flush-count: 10 request-logfile-max-size: 1000000 request-logfile-max-files: 10 include: 6connect_nsd.conf |
[authdnsadmin@Secure64DNS]# mkdir test12 [authdnsadmin@Secure64DNS]# ls /: 322 2013-08-19 06:07:42 nsd.conf <DIR> 1024 2013-08-16 17:30:12 test12 |
Go to the 6connect Admin area and click on the DNS Admin Tab. Click on the New Server button.
Then fill in the information for your Secure64 server (including any relevant SOA information):
Press the Test Config button for the DNS Server you setup.
Success! Will show as depicted above.
Click Add Server to add this server as a permanent entry in the dropdown menu. This server will now be available for assigning DNS zones to.

Select the "Bulk DNS Change Tools" link under the DNS Defaults and Tools section of the page.

Search for all available zones or enter in a value to find specific existing zones in the system. Click the "Match" button to see results.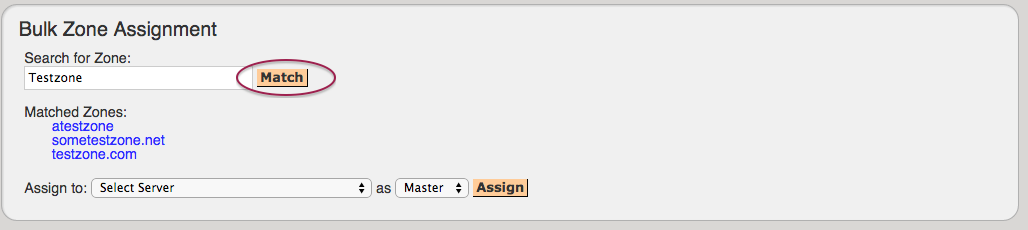
No character in the search area indicates a search for all zones |
Select the Secure64 server under Assign To, choose whether as a Master / Slave, and hit "Assign" to assign the above zones to this server.
Under DNS Zone Transfers, verify the server and the zones to transfer. To view the zone names, click on the # Zones link next to the server.
Check the # Zones box and click on the Push button to transfer the zones to this server.
The system will present the following live progress bar.
Towards the bottom of the progress status will be the final indication of success or errors to correct.
The result of the Push can be checked/verified by checking the Secure64 server as follows:
| ssh to 50.198.192.141 Login using the designated login account and password Enable cachednsadmin ls |
Now, verify that the "788 2013-08-21 12:35:04" 6connect_nsd.conf file now exists.
[authdnsadmin@eval138.secure64.com]# ls /: 6728 2013-08-13 00:15:30 nsd.conf 8416071 2013-08-21 12:35:07 nsd.db 788 2013-08-21 12:35:04 6connect_nsd.conf <DIR> 1024 2013-08-21 12:34:50 test12 |
You can verify the Push contents by doing a cat of the 6connect_nsd.conf
[authdnsadmin@Secure64DNS]# cat 6connect_nsd.conf AutoGenerated by 6connect ProVision. Do not manually edit. zone: name: atestzone.com zonefile: /test12/6connectGeneric/m/atestzone.com.zone zone: name: Testzone2.com zonefile: /test12/6connectGeneric/m/Testzone2.com.zone |
In the example above, two Zones have transferred.
To look at the contents of each zone you can cd to the proper directory /test12/6connectGeneric and find the zone files in an alphabetical directory structure as follows:
[authdnsadmin@Secure64DNS]# cd 6connectGeneric [authdnsadmin@Secure64DNS]# cd test12 changed to test12 |
Finally, do a dig of the zones to verify the DNS configuration has been successfully deployed.
| [authdnsadmin@eval138.secure64.com]# dig @50.198.192.141 atestzone.com ; ﹤﹤﹥﹥ DiG SourceT 3.x ﹤﹤﹥﹥ @50.198.192.141 atestzone.com ;; Got answer: ;; ﹥﹥HEADER﹤﹤ opcode: QUERY, status: NOERROR, id: 59591 ;; flags: qr aa rd; QUERY: 1, ANSWER: 0, AUTHORITY: 1, ADDITIONAL: 0 ;; QUESTION SECTION: ;atestzone.com. IN A ;; AUTHORITY SECTION: atestzone.com. 3600 IN SOA ns1.dns.6connect.net. hostmaster.6connect.net. (2013082102 10800 3600 604800 38400 ) [authdnsadmin@eval138.secure64.com]# |
For any questions regarding the integration of Secure64 products into 6connect ProVision, please email 6connect at support@6connect.com, or Secure64 at support@secure64.com